.
The NIS2 Directive: Evolution, not revolution – or how to avoid falling into the ‘cyber-fear’ trap?
“Cyber-fear” as a business model
Recently, in the media and online, there has been a proliferation of materials, articles and comments regarding the NIS2 Directive. Some of these are valuable and substantive, but there are also those aimed at appealing to our primal instincts – they seek to instil fear in us. As I have been more or less professionally involved with the utilities sector over the years, this approach strikes me as somewhat jarring, and I feel compelled to address this issue. This is not a method of building a business that I accept. Education? Yes. Instilling fear? No.
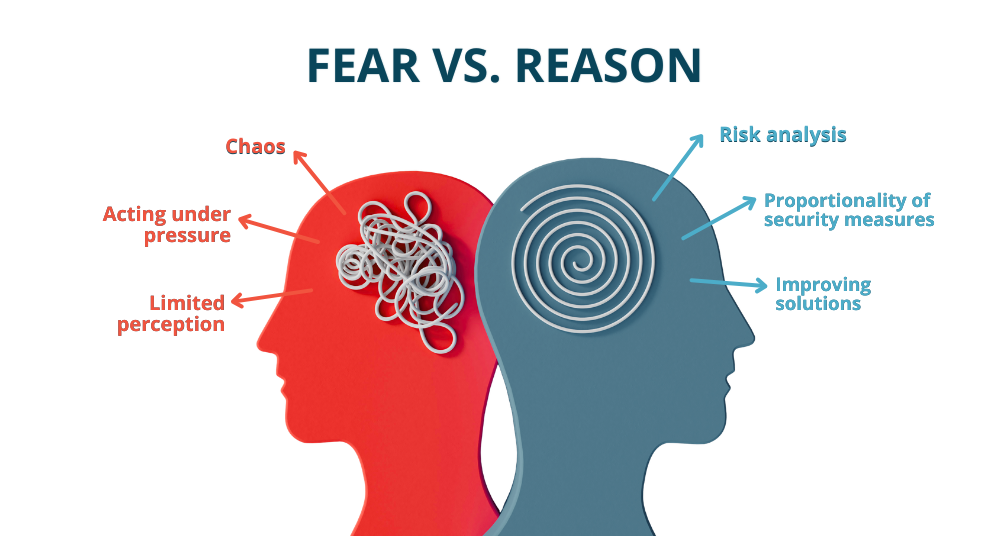
Building reach based on emotions is quite a common practice these days. The audience readily responds to catchy slogans and headlines that need not have much to do with the truth. Under the influence of emotions, especially strong ones, people also tend to make quick, but not always beneficial, decisions. The ‘grandchild’ and ‘bank call’ scams that have been widely publicised in recent years are based on similar social engineering mechanisms. You are afraid, you are acting under pressure, so your perception and ability to assess the situation objectively are limited, yet you must act quickly. You see no other option than the one offered to you by the sender of the message…
The Foundations of Cybersecurity
Let me start by saying that cybersecurity in the broadly defined utilities or public sector has always been synonymous with the security of the state, society and the economy. Until recently, the NIS Directive was in force; it is now in force in its NIS2 iteration. And before that? Exactly… Were there no cybersecurity threats to critical infrastructure before? There were. Was there chaos and cyber anarchy before? No. Were there no regulations in place? There were. Take, for example, the National Interoperability Framework (KRI) standards in force since 2012, which imposed an obligation on public entities to implement an Information Security Management System (ISMS).

So why all this lamentation and confusion following the national implementation of NIS2?
For many years, there have been local and international standards, norms and regulations that outline best practices or requirements in the areas of security, cybersecurity (e.g. ISO 27001) and business continuity (e.g. ISO 22301).
Crucially, these are updated from time to time to enhance their effectiveness and adapt to the rapidly changing world around us. If someone has been following the previous requirements, they are not facing a revolution, but an evolution. However, if someone has not been following them, they have a problem, but how to put it as diplomatically as possible – the cause is not NIS2 itself.
Why is there so much talk about this now?
The topic of cybersecurity has been strongly and constantly (that is the key word) highlighted to the public more or less since the outbreak of war on our eastern border. Previously, there were media reports and articles, but these were more of a ‘filler’ for airtime and concerned only those spectacular (media-friendly) attacks, such as ransomware attacks on medical facilities.
Although the reasons for the current state of affairs are tragic, it is good that we have started talking about cybersecurity and it is good that mandatory regulations are coming into force, because security at the national or EU level cannot be optional. It is a bit like fire safety regulations applying only to selected flats in a block of flats. A fire won’t break out in my flat, but what’s the point if one does in my neighbour’s flat one floor below.
Returning to the issue of the confusion caused by the national implementation of the NIS2 Directive, in my opinion, one cannot be surprised by the fact of the Directive’s implementation and its consequences, because:
Standards and requirements already existed previously, providing a solid foundation. Our national implementation of NIS2 is significantly delayed compared to the EU directive itself, and the ‘framework’ has been known for some time.
At the same time, one cannot underestimate the scope of the changes resulting from NIS2 (including):
- Comprehensive risk management – threats are not limited to cyberattacks.
- Management commitment and accountability – gone are the days when an “IT specialist” with no decision-making power or allocated budget was responsible for cybersecurity.
- Strict reporting regime – everything must run like clockwork to meet the requirements.
- Business continuity – for instance, by including the supply chain within the scope of the directive.
Low barriers, or where the real problem lies
Some will raise a wide range of arguments, such as staff shortages, costs, investment needs, and the duration of tender procedures.
Yes, but… many aspects of NIS2 were and still are achievable without the need for significant investment. I am referring, for example, to: ensuring the supply chain consists of ‘secure’ suppliers, utilising security mechanisms already available in currently used solutions – perhaps not yet utilised for some reason – reviewing them, regular software updates, educational initiatives, the use of individual passwords and their periodic change, including following staff changes, the use of individual PIN codes for SIM cards, preferably 6-digit rather than 4-digit codes, just in case. There are plenty of readily available solutions, and as the available data shows (source: https://projektik.eu/cyberataki-na-sektor-wod-kan-w-polsce-stan-na-pazdziernik-2025/ accessed: 06/03/2026), attack vectors occur via so-called ‘low fences’ – remote access (RDP, VNC, TeamViewer), weak passwords, lack of IT/OT segmentation, for which solutions do not require directives and equipment on a par with the National Bank of Poland, but rather common sense and a moment of self-reflection.
Audits and penetration tests are snapshots of reality. Ensuring cybersecurity is a feature film. It is not possible to ‘secure’ a system once and for all, but one must ‘secure’ it continuously, as threats are constantly evolving.
Furthermore, NIS2 is based on risk analysis and proportionality (another key word) of the solutions implemented. One of the key issues is to conduct risk analysis and plan measures to eliminate risks or reduce them to an acceptable level. These measures do not have to be implemented ‘here and now’, though fortunately they cannot be postponed indefinitely. It is permissible, indeed required, to identify, catalogue and assess risks (i.e. conduct an analysis), and then plan the necessary measures. These measures may depend, amongst other things, on the availability of budget and staff, and may also be deferred for objectively justified reasons. However, they must not be ignored or left unmanaged.
The narrative of an impending Cyber-Armageddon, the inevitability of NIS2 implementation, multi-million-pound investments and the looming spectre of penalties for non-compliance, is fuelling and will continue to fuel speculation in the cybersecurity products and services market, particularly within the utilities sector. There is a finite number of suppliers on the market, and ‘self-proclaimed NIS2 experts’ are already springing up like mushrooms after rain. The services and products currently on offer will often be excessive in relation to the capabilities of entities covered by NIS2, particularly in terms of price.
But wouldn’t you shell out an extra few tens of thousands if the spectre of personal liability loomed over you? That fear again…
Why am I writing about this, and why in this way?
I am writing because I do not agree with this method of building business relationships. I work in a team where we understand professionalism as the ability to tell the truth, even if it means a lower invoice value. We believe that long-term business relationships are built on professionalism and mutual trust, not on preying on ignorance or speculation under the guise of ensuring compliance with this or that directive. That is how I operate personally, and that is how our team operates.
We have already seen a glimpse of the inadequacy and irrationality of implementations in the ‘cybersecure water supply’ programme, where small waterworks purchased (on recommendation?) cybersecurity systems ‘just under the funding limit’ through tender procedures – systems that even large, highly advanced companies in terms of cybersecurity would not be ashamed of. Everything is in order, because the programme’s rules were formally met, the idea was lofty, and the IT equipment was purchased and implemented. Yet in stark contrast to this super-advanced IT solution operating in a high-availability cluster, generating alerts at the slightest deviation, there are staff and skills shortages to operate these systems, almost universally accessible drinking water supply points with no monitoring whatsoever—not even of a well manhole cover—or PLC controllers that have been in operation for 15–20 years, which are in no way networked or use obsolete technologies such as 2G, and are often never updated with firmware. But this element could not be subsidised by the programme, at least not directly. Similarly, we could install certified, burglar-proof doors and windows in our homes, only to leave them ajar when we go out.
Nor should we forget that whilst there was funding for CAPEX (capital expenditure), these solutions will still need to be maintained over time (OPEX), i.e. renewing licences and technical support in subsequent years, which account for a significant percentage of the purchase price of these systems. To continue with the analogy to everyday life, it’s like winning an expensive car in the lottery but not having the means to maintain it.
I strongly urge you to keep a cool head and use common sense amidst this information frenzy. This will allow you, dear readers, to plan your actions and spend your resources rationally on those aspects and elements that truly require the most urgent attention, and this will have the greatest impact on improving security. Do not be guided by emotions or fear, for fear is not a good advisor. NIS2 does not force you to implement the most advanced and secure cybersecurity solutions. They must be adequate (proportionate) to the risk, the area, and the exposure.
NIS2 compels us to address the issue of cybersecurity in a conscious, continuous, responsible and proportionate manner.
Which path will you follow?
Read more articles:

Why are dedicated M2M SIM cards crucial in telemetry?
Check the differences, formalities and APN security

Inventia is delighted and proud to announce that it has obtained certification for compliance with the ISO/IEC 27001 standard
Read the article and find out more about the Information Security Management System certification






